How to create a bootable macOS Sierra installer drive
![]()
Apple uses its App Store to distribute its software, like new Mac operating systems. It’s convenient, but sometimes it can take a while for a download to finish. And if you have multiple Macs, it’s inefficient to download the new OS to each and every Mac.
That’s why I like to make a bootable external drive for the sole purpose of installing the Mac operating system. When I need to tend to a bunch of Macs, it’s much faster to use a bootable drive instead of going to each Mac, launching the App Store, searching for the operating system, downloading it (after entering my Apple ID), and then running the installer.
You can create a bootable USB flash drive with the macOS Sierra installer that’s now available. The installer software will take up nearly 5GB of storage space. Here’s how to create a bootable macOS Sierra installer drive.
Macworld also has bootable-install-drive instructions for El Capitan (OS X 10.11), Yosemite (OS X 10.10), Mavericks (OS X 10.9), Mountain Lion (OS X 10.8), and Lion (OS X 10.7).
Download the macOS Sierra installer
Launch the App Store app, then look for macOS Sierra in the store. (Here’s a link.) Click on the Download button, and your Mac will download the installer to your Applications folder. If it automatically launches after download, quit the installer.
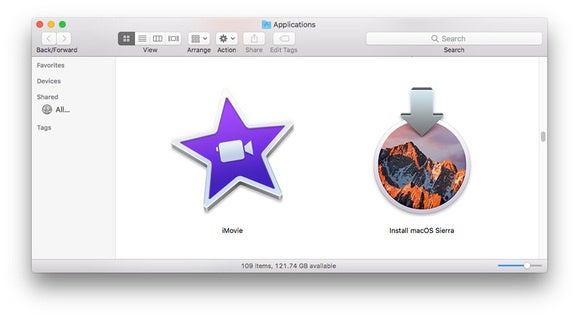
If you’ve already upgraded your Mac to Sierra, the installer is removed from the Applications folder. You can download it again if you go to Purchased in the App Store. Look for macOS Sierra in the list of apps that you’ve bought, and click on the Download button. If it automatically launches after download, quit the installer.