Connect to Blocked Ports with SSH Tunneling
SSH Tunneling – Get Through Your Firewall to Other Ports

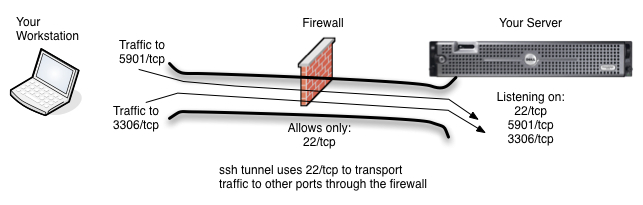
Typical Scenario is that only the ssh port (tcp/22) and http (tcp/80) are allowed into a machine. All other traffic is blocked.
Do you have a server on the other side of a firewall that you can ssh to, but to which you cannot reach on other ports. Let’s imagine, for example, that your server has ports 80/tcp and 22/tcp open, but you want to be able to get to your database port (3306/tcp) or your vnc port (5901/tcp) which are blocked by the firewall. Grr. What can you do? Use ssh tunneling, of course.
SSH Tunneling is Similar to VPN
Ssh allows you to tunnel your communication to other ports and services on your server through your ssh connection to the server. This means that traffic that would normally be blocked by your firewall or iptables can now reach its destination. This of course, all assumes that you have a login to the server and are able to ssh to it from your network or internet location.
SSH Tunneling Uses a Local Port
The idea behind ssh tunneling is that you know which port(s) you want to access on the server and that you also setup a local port on your workstation for you to connect to on your side of the tunnel. When using SSH Tunneling, you will direct your client applications, in this example case MySQL Workbench and VNC Viewer, to the local ports on your workstation which you configured in your ssh client. SSH will then transport the traffic to the local port through its tunnel to the server port you are hoping to reach.
Ssh Command Line (CLI) Port Configuration
When using ssh from the command line in a linux, unix, OSX or other command line environment, you will use the -L option to map local ports to remote ports on the server. In the example below, Mary is logging in to server1.uptimemadeeasy.com with ssh and is mapping local port 8675 on her workstation to the MySQL port (tcp/3306) on the server. Note that the name localhost is in reference to server1.uptimemadeeasy.com.
ssh -l mary server1.uptimemadeeasy.com -L 8675:localhost:3306
Mary will then supply the password when requested and she will notice with netstat -an that port 8675 on her local workstation is now being used. She can then point her MySQL Workbench client at her local machine (localhost) port 8675. Her traffic to her local port 8675 will then be transported through her ssh tunnel to the server port 3306.
Mary can now verify that her local port (8675) is listening locally using netstat:
$ netstat -an | grep 8675
TCP 127.0.0.1:8675 0.0.0.0:0 LISTENING
TCP [::1]:8675 [::]:0 LISTENING
We get output telling us that the local workstation is now listening on port 8675 on both ipv4 and ipv6. Lire la suite…